Emotet has updated the C2 comms in the latest release, going for URIs instead of IPs (root).
Here’s a complete list of the current campaign:
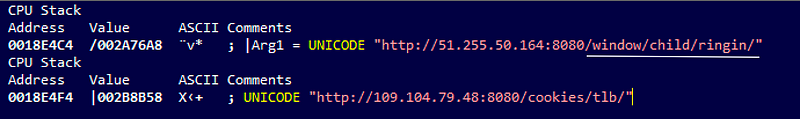
Emotet C2i:
http://51.255.50.164:8080/window/child/ringin/ http://109.104.79.48:8080/cookies/tlb/ http://92.48.118.27:8080/rtm/pnp/ http://197.248.67.226:8080/enabled/forced/ http://181.170.93.38:8080/teapot/balloon/ http://69.163.33.82:8080/glitch/scripts/arizona/ http://192.155.90.90:7080/prov/odbc/arizona/ http://43.229.62.186:8080/teapot/ http://72.47.248.48:8080/sess/cone/ http://209.159.244.240:443/publish/vermont/tlb/ http://197.248.67.226:8080/codec/between/tlb/ http://176.58.93.123:8080/splash/ http://72.47.248.48:8080/sess/glitch/entries/ http://181.170.93.38:8080/schema/free/ http://69.163.33.82:8080/badge/symbols/results/ http://109.73.52.242:8080/results/prov/ http://68.191.37.107/iplk/vermont/sym/merge/ http://154.120.228.126:8080/xian/enabled/sym/merge/ http://136.49.87.106/usbccid/taskbar/enabled/ http://5.9.128.163:8080/json/balloon/enabled/merge/ http://5.9.128.163:8080/taskbar/odbc/window/ http://192.155.90.90:7080/sess/balloon/pnp/merge/ http://99.243.127.236/window/tlb/symbols/ http://43.229.62.186:8080/taskbar/badge/symbols/merge/ http://176.58.93.123:8080/health/ http://181.44.231.127:443/window/iab/symbols/merge/ http://209.159.244.240:443/odbc/srvc/report/ http://190.117.206.153:443/glitch/raster/guids/ http://74.36.4.206/splash/attrib/guids/merge/ http://69.163.33.82:8080/balloon/img/ http://190.117.82.103:443/merge/jit/taskbar/merge/ http://51.255.50.164:8080/results/usbccid/taskbar/merge/ http://165.227.213.173:8080/odbc/iplk/ http://154.120.228.126:8080/enable/usbccid/child/ http://200.125.190.126:8080/mult/mult/ http://186.139.160.193:8080/prep/rtm/child/ http://192.155.90.90:7080/glitch/symbols/child/merge/ http://187.189.210.143/enable/chunk/child/merge/ http://72.47.248.48:8080/enable/rtm/child/ http://209.159.244.240:443/publish/forced/child/merge/ http://200.114.142.40:8080/devices/mult/child/ http://74.36.4.206/acquire/acquire/child/ http://144.76.117.247:8080/balloon/pdf/child/ http://109.73.52.242:8080/loadan/glitch/child/merge/ http://139.59.19.157/merge/sess/ http://181.44.231.127:443/usbccid/balloon/child/ http://67.241.81.253:8443/cab/entries/ http://200.114.142.40:8080/nsip/ringin/ http://74.36.4.206/walk/ http://144.76.117.247:8080/iplk/health/ http://69.163.33.82:8080/codec/ http://99.243.127.236/merge/chunk/ http://187.189.210.143/devices/child/usbccid/ http://72.47.248.48:8080/xian/sess/usbccid/ http://67.241.81.253:8443/merge/balloon/raster/ http://190.117.206.153:443/attrib/usbccid/ http://74.36.4.206/pdf/teapot/raster/ http://144.76.117.247:8080/scripts/splash/acquire/ http://192.155.90.90:7080/attrib/walk/acquire/merge/ http://104.2.2.153:8080/balloon/merge/ http://62.75.143.100:7080/pdf/child/rtm/ http://67.241.81.253:8443/arizona/entries/rtm/ http://197.248.67.226:8080/schema/health/rtm/ http://74.36.4.206/between/teapot/walk/ http://69.163.33.82:8080/loadan/report/ http://99.243.127.236/raster/bml/ http://43.229.62.186:8080/iab/chunk/walk/ http://72.47.248.48:8080/stubs/ban/teapot/merge/ http://67.241.81.253:8443/symbols/codec/tpt/merge/ http://200.114.142.40:8080/site/forced/ http://74.36.4.206/cookies/enable/ http://144.76.117.247:8080/enable/raster/balloon/ http://192.155.90.90:7080/taskbar/report/balloon/merge/ http://187.189.210.143/scripts/attrib/ http://62.75.143.100:7080/vermont/ http://68.191.37.107/scripts/taskbar/ http://136.49.87.106/cone/health/balloon/ http://210.2.86.72:8080/dma/bml/ http://5.9.128.163:8080/bml/xian/ http://190.0.32.206:8080/entries/iplk/balloon/merge/ http://138.68.139.199:443/srvc/prep/ http://89.211.193.18/pdf/report/cookies/merge/ http://200.125.190.126:8080/scripts/window/enable/merge/ http://186.139.160.193:8080/window/merge/ http://219.94.254.93:8080/forced/loadan/ http://201.165.102.49:443/jit/raster/enable/ http://192.163.199.254:8080/publish/dma/enable/merge/ http://138.68.139.199:443/glitch/ http://68.191.37.107/splash/merge/enable/ http://184.160.113.4/psec/free/enable/ http://67.241.81.253:8443/teapot/
Comments
Post a Comment